How to conduct a Twitter OSiNT investigation like a pro
This blog post will assume that you already know what is and how OSiNT works. If you do know what it is, then you can begin reading.

Twitter open source intelligence. How do we do it? This is a great question and it should interest you as an information gatherer because Twitter is one of the most popular social media platforms at this moment . We can rest assured say that most of us own an account on the platform . How we, as information gatherers conduct a Twitter OSiNT investigation ?
- We do NOT use the Twitter’s API. Why you ask? Well this should be self-explanatory . Twitter has limits. Even though all you are doing is 100% legal, or I just hope it is, Twitter believes that you are up to no good and from a machine’s perspective you are definitely a threat when you are scrolling at 100 mph on a person’s account . So please, avoid using the Twitter’s API .
# twint
- What is it ?
-> Well then, what do we use? We SCRAPE Twitter. You might think that you are in the wrong place but you are not . You won’t need to program nothing at all because with the folks at twintproject, we have twint. An advanced Twitter scraping tool coded in Python that allows you to scrape tweets from Twitter and much more WITHOUT using the Twitter API. This ensures , that you can 100% scroll at 800 mph and you WON’T get blocked by Twitter where as with Twitter API, you will get blocked at about a few hundred tweets.
- LIMITS
-> “Twitter limits scrolls while browsing the user timeline. This means that with .Profile or with .Favorites you will be able to get ~3200 tweets.”- — twintproject GitHub page.
- GitHub page
-> https://github.com/twintproject/twint
- Slight problems with twint
- > The main problem some of the users have with it is the fact that they have to keep up with all the flags for instance, in order to perform a VERY basic investigations on a person’s account , here’s what you need to do : “twint -u username” or “twint — username username”. And that will just be a very basic ‘investigation’. Then there comes all the hard flags when you want to filter the results and all that good stuff so I came up with a solution to this even though you can definitely learn those flags AND YOU SHOULD! Don’t be a script kiddie.
# twosint
-> twosint is a Twitter OSiNT investigation tool that automates twint . It’s a 300+ lines Python3 code that automates a lot of the stuff by cutting all the flags into modules. At first it was just a lame script that just automated things but now it has become a console . Yes, you can use it as a ‘terminal’ in that you can set things, unset things , get the current username , exit, clear, get information on modules, set modules and all that good stuff.
- LIMITS
-> Well, since this currently ONLY relies on twint , it has the same limits.
- GitHub page
-> https://github.com/c0m3t-k2/tw1tter0s1nt
- Problems with twosint
-> The only problem APART from the problems with twint since it relies on it like I have mentioned before, is the fact that at times it can be quite unstable. I am the only person contributing to this project and it is quite hard to keep up with all the updates. However I have pretty much bypassed this issue by adding a beta and an official file for instance “twosint.py” & “twosint_beta.py” and you guessed it, the beta file includes the latest updates and the official file includes less features but offers stability instead . If you are a quite experienced Python3 programmer you can definitely contribute to this open soruce project.
# demonstration
- After you follow the https://github.com/c0m3t-k2/tw1tter0s1nt installation steps for both twint and twosint then you can begin.
- First of all , let’s run the tool : python3 twosint.py
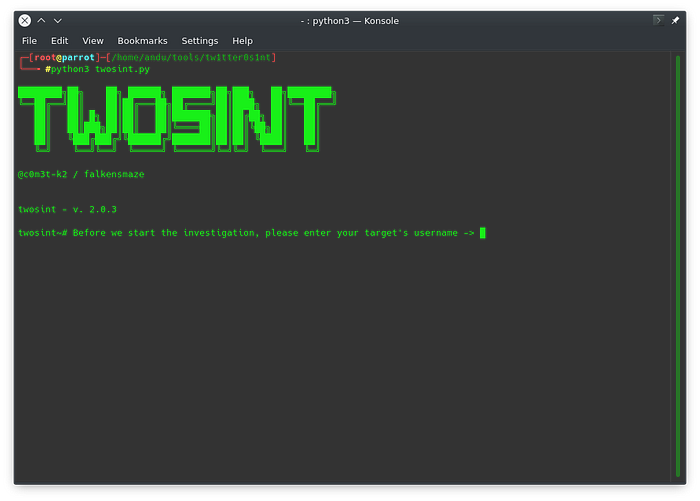
- Then, type in a username for instance ‘networkchuck’ <sorry chuck>
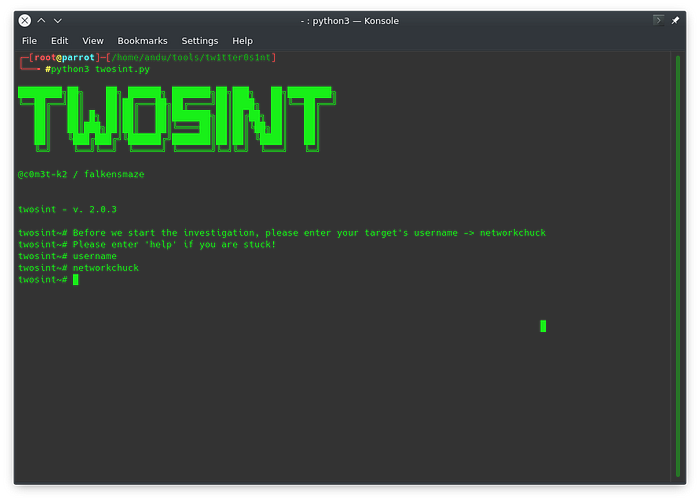
We can assure we have typed it in correctly by putting the command ‘username’ in it.
- Now, let’s type ‘help’ to see what happens :)

We get all of these commands. I recommend studying them for a second to see what each one does. Obviously the most interesting ones are ‘modulebomb’, ‘run [modulename]’ and ‘info [modulebomb]’. So let’s do that
- Let’s modulebomb
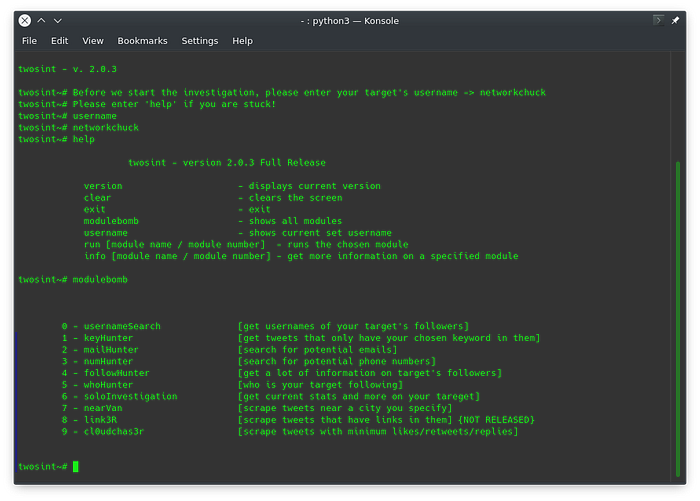
Woah, a lot of good modules right? Yeah, that is why even I prefer to use my OWN tool over twint, it just makes your life easier in my opinion.
What I am going to perform is a soloInvestigation (number 6) in order to make this blog post shorter.
- So firstly let’s do info ‘soloInvestigation’ and then run it.
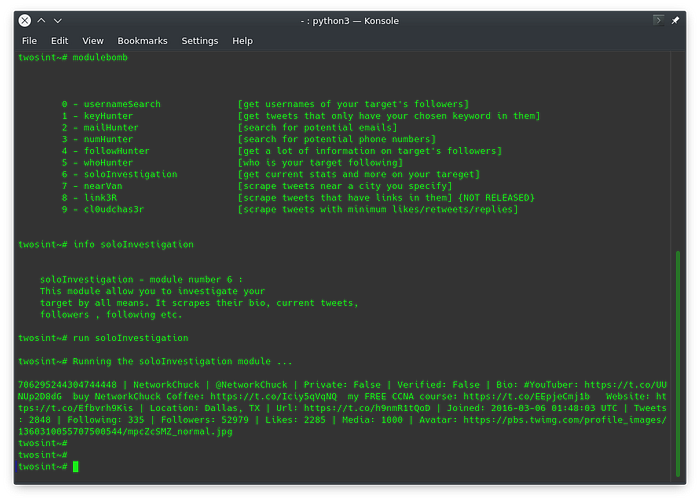
So , firstly we have run the ‘info’ command and you can see the output . It gives us a description on the module .
Then, we’ve run the ‘run’ command and you can see the output . We got a lot of information on our so called target. This information can help you later. However, you can definitely see that there are so many more modules that you can try out .